Hi, I’m Samuel Idire

Protecting Digital Frontiers, One Risk at a Time
Cybersecurity Analyst & GRC Specialist | Expert in Risk Control | Compliance | Threat Mitigation
Know More About Me
I’m a passionate Cybersecurity Analyst and GRC Professional with a strong foundation in security governance, risk assessment, and compliance management. With hands-on experience in both the technical and strategic side of cyber defense, I help organizations stay ahead of threats and aligned with evolving regulatory standards.
My Professional Experience
Cybersecurity Analyst Intern
AMDARI
(Jun 2024 – Dec 2024)
Assisted in threat intelligence monitoring and incident response. Contributed to policy documentation and compliance audits. Gained experience in SIEM tools and endpoint protection.
Cybersecurity Specialist & GRC Analyst
10Alytics
(Jan 2025 – Present)
Developed risk frameworks and implemented controls aligned with ISO 27001 and NIST. Conducted vulnerability assessments and reported on compliance status. Worked with cross-functional teams to maintain security posture.
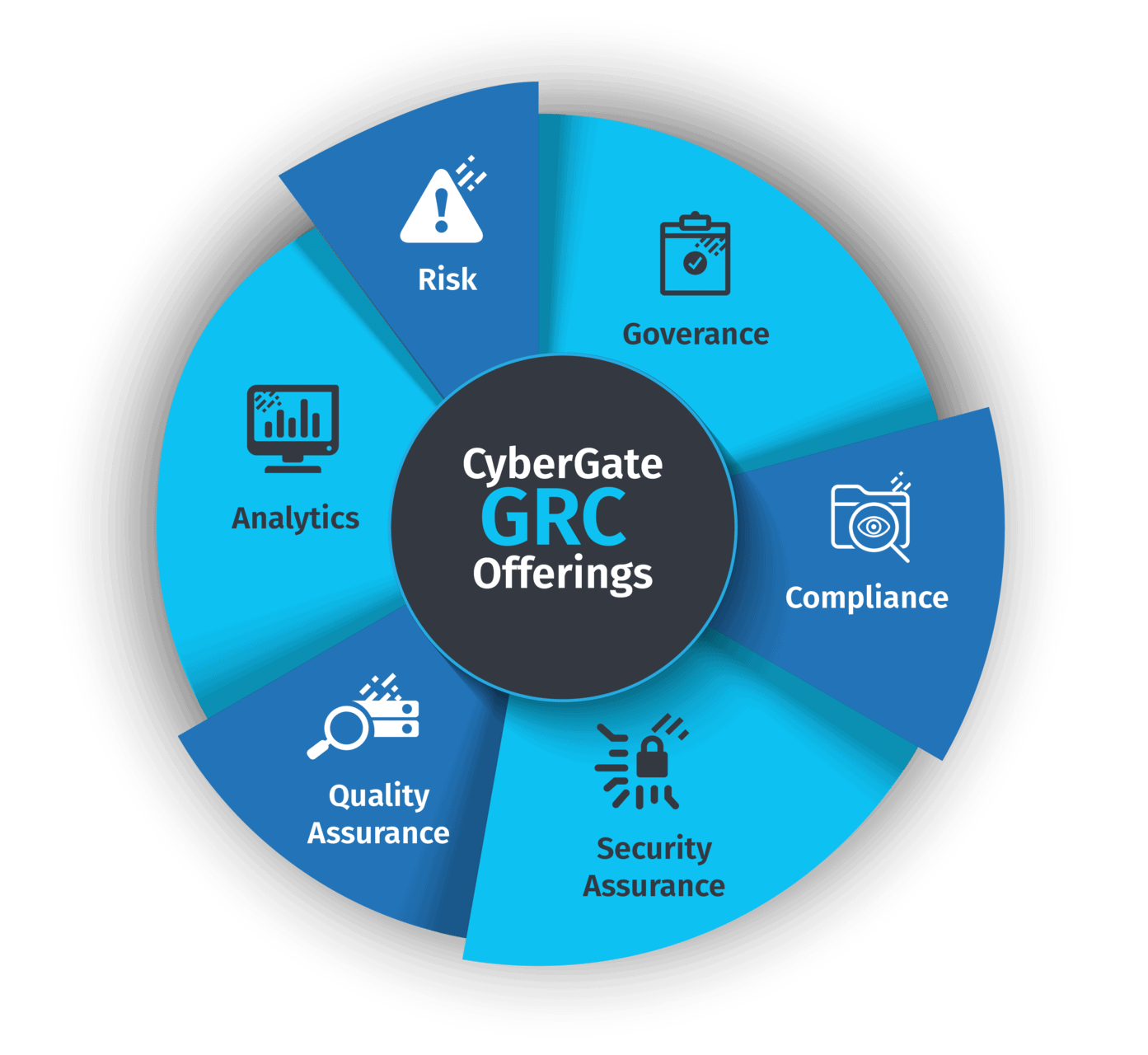
My Core Competencies
- Risk Assessment & Control
- GRC Tools (e.g., ServiceNow, Archer)
- Security Auditing
- SIEM (e.g., Splunk, IBM QRadar)
- Vulnerability Management
- NIST, ISO, SOC 2 Frameworks

Case Study 1
Early Detection of a Cyber Attack on a Healthcare Company Website – $20M Loss Prevented
Background
In early 2024, I was part of the cybersecurity team responsible for monitoring and maintaining the digital integrity of a major healthcare organization’s public-facing website. The company hosted sensitive patient information through a secure portal and was a known target for threat actors due to its size and industry profile.
The Situation
During a routine threat intelligence and anomaly monitoring task, I noticed an unusual pattern of traffic coming from a previously unseen IP range located outside the company’s usual geolocation zones. The activity mimicked normal user behavior but with subtle inconsistencies—such as unusually timed login attempts, extended session durations, and indirect probing of admin-level endpoints.
Investigation & Response
I initiated a real-time investigation and cross-referenced the IP addresses with known indicators of compromise (IoCs). Using network traffic analysis tools and the organization’s SIEM (Security Information and Event Management) system, I detected a slow-moving brute-force attack paired with reconnaissance attempts—classic hallmarks of a credential stuffing attack aimed at compromising patient accounts.
I immediately:
• Alerted the SOC (Security Operations Center) team.
• Recommended temporary IP geofencing and rate-limiting on the targeted endpoints.
• Collaborated with the DevSecOps team to implement CAPTCHA and MFA (multi-factor authentication) escalation on affected login flows.
• Coordinated a deep-dive forensic analysis of server logs and deployed a temporary honeypot to study attacker behavior.
Outcome
The attack was contained before any data was breached. Post-incident simulations and audits showed that if the threat had gone undetected for another 48–72 hours, the attackers would likely have accessed thousands of patient records.
Given the high costs of healthcare data breaches—including legal settlements, fines, identity protection services, and loss of trust—the organization estimated a potential exposure of over $20 million in compensation and remediation costs.
Impact
• Zero data loss or exposure
• Full mitigation within 6 hours of detecti0o0n
• $20M in projected losses prevented
• Improved incident response protocol based on lessons learned
• Implemented new proactive traffic anomaly detection rule in the SIEM
Key Takeaways
This incident reaffirmed the critical role of proactive monitoring and swift cross-functional collaboration in cybersecurity. It also highlighted how small anomalies—if taken seriously—can prevent massive breaches.
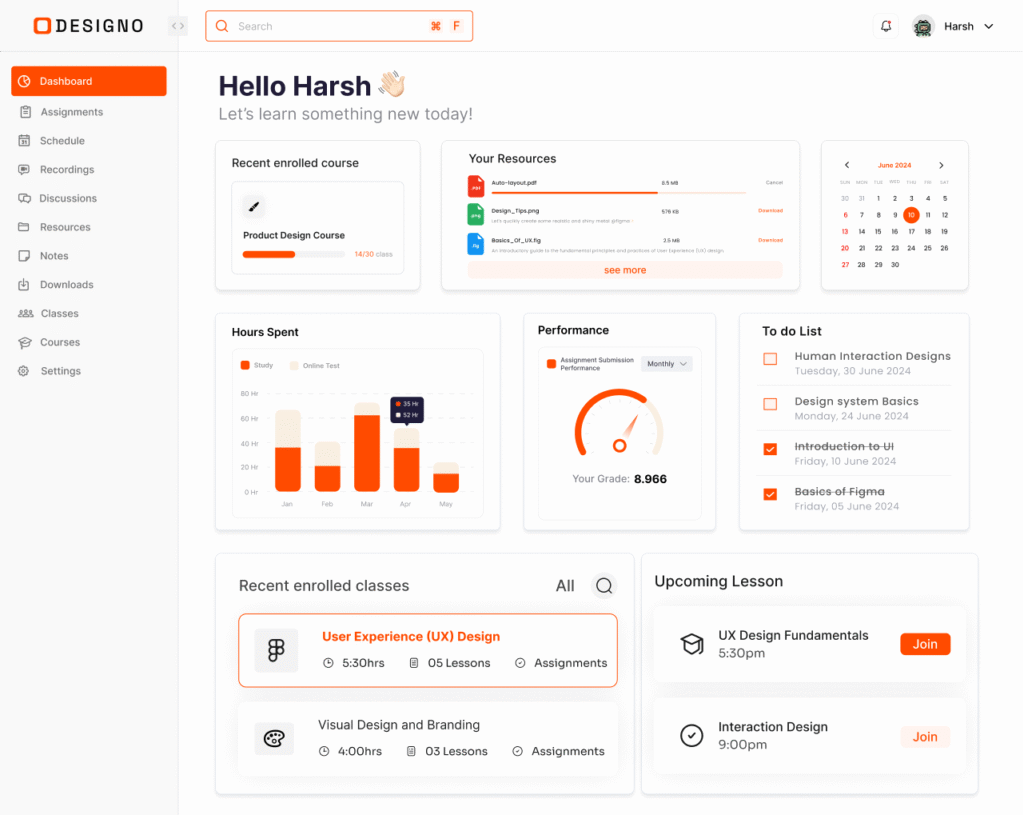
Case Study: Enhancing Cybersecurity Governance & Compliance
Mid-sized healthcare org. undergoing digital transformation. Needed governance alignment with NIST & ISO 27001 while ensuring HIPAA/PHIPA compliance.
Objectives:
- Identify cybersecurity gaps.
- Implement risk-based GRC program.
- Improve compliance tracking.
- Reduce audit prep time by 40%.
Key Actions:
– Conducted NIST & HIPAA gap analysis.
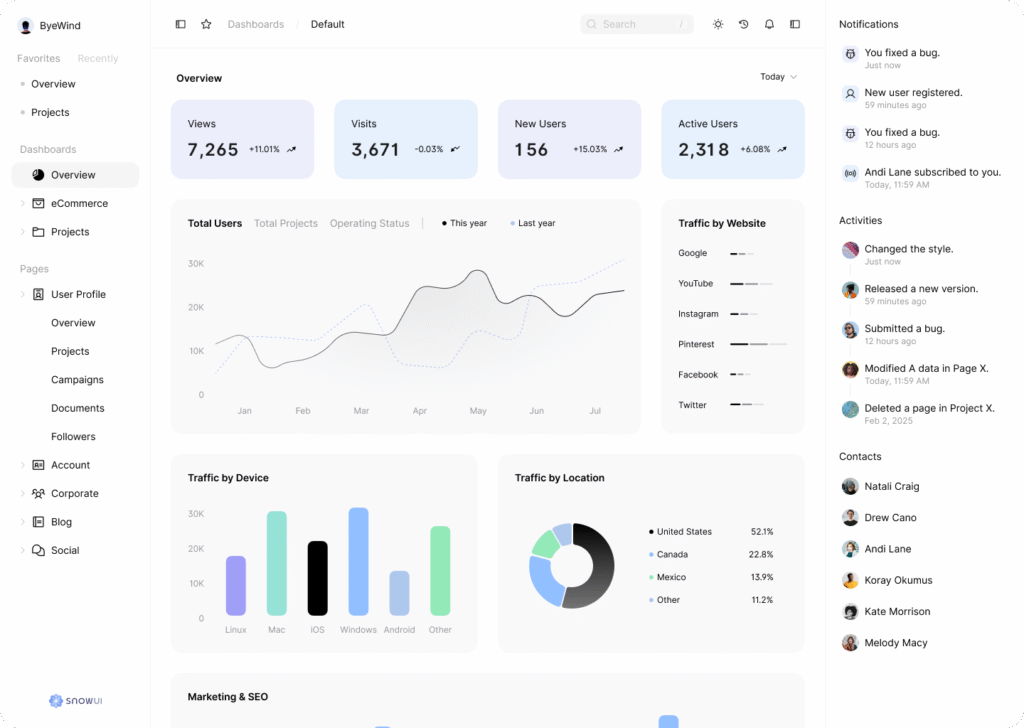
– Created GRC dashboard in Power BI.
– Developed vendor risk policies.
– Automated compliance checks.
– Ran ransomware response exercise.
Results:
– Reduced audit prep time by 60%.
– Closed all high-risk vulnerabilities.
– Cut vendor assessment time by 45%.
– Increased compliance training completion to 98%.
Skills Demonstrated: Risk Assessment • Regulatory Compliance • Policy Development • GRC Dashboard Creation • Incident Response
Let's create amazing stuff together!
Have a project in mind? Looking to partner or work
together? Reach out through the form and I’ll get
back to you in the next 48 hours.